Home Network Security: Firewalls, VPNs, and Intrusion Detection for Beginners
By Alex Torres | March 1, 2026 | Network & Privacy
A beginner-friendly guide to locking down your home network with a proper firewall (pfSense or OPNsense), WireGuard VPN for remote access, Suricata IDS for threat detection (see our Tailscale VPN setup), and DNS security best practices.
Your ISP Router Is Not Enough
Let me start with the uncomfortable truth: that router your ISP handed you when they set up your internet connection is one of the weakest links in your home network security. I used to trust mine completely. It had a password on the Wi-Fi, it had a basic firewall checkbox in the settings (see our Pi-hole DNS filtering) (see our Cisco IOS comparison), and I figured that was good enough. I was wrong.
ISP-provided routers have serious problems that make them unsuitable as your primary line of defense:
- Infrequent firmware updates — many go months or years without patches, leaving known vulnerabilities wide open.
- Default credentials — they often ship with well-known admin passwords that users never change.
- Limited firewall rules — most offer a simple on/off toggle with no granular control.
- No intrusion detection or VPN server capability.
- Remote management backdoors — ISPs often retain remote access, creating an attack surface you cannot control.
The good news is that building a proper home network security setup is more accessible in 2026 than it has ever been. Affordable hardware, mature open-source software, and excellent community documentation mean you can have enterprise-grade protection for the cost of a used mini PC. In this guide, I will walk you through the core components: a real firewall, a VPN for secure remote access, an intrusion detection system, and DNS-level security.
Choosing Your Firewall: pfSense vs. OPNsense
The firewall is the foundation of your network security. It controls what traffic enters and leaves your network, segments your devices into isolated zones, and gives you visibility into what is actually happening on your LAN. For a home firewall setup, two open-source platforms dominate the conversation: pfSense and OPNsense.
pfSense
pfSense has been around since 2004 and has one of the largest communities in the open-source firewall space. It is based on FreeBSD with a powerful web-based interface. pfSense Community Edition (CE) is free, and its strengths include a massive library of community tutorials, a mature package system (Snort, Suricata, pfBlockerNG, OpenVPN), and a long track record in production environments.
OPNsense
OPNsense forked from pfSense in 2015 and has carved out its own identity with a more modern UI, a built-in plugin system, weekly security updates, and native WireGuard support. I run OPNsense on a Protectli VP2420 mini PC with four Intel NICs, and it has been rock solid. Either platform will serve you well: pfSense for community resources and battle-tested reputation, OPNsense for a cleaner interface and native WireGuard.
Hardware You Will Need
You do not need expensive gear. Here is what I recommend for a home firewall setup in 2026:
- Mini PC — a Protectli, Qotom, or even a used Dell OptiPlex Micro with at least two Ethernet ports. Aim for an Intel Celeron N5105 or better, 4 GB RAM minimum (8 GB if you plan to run Suricata IDS), and a 64 GB SSD or eMMC.
- Two Ethernet ports minimum — one for WAN (internet), one for LAN. More ports let you create additional network segments (IoT VLAN, guest network, lab network).
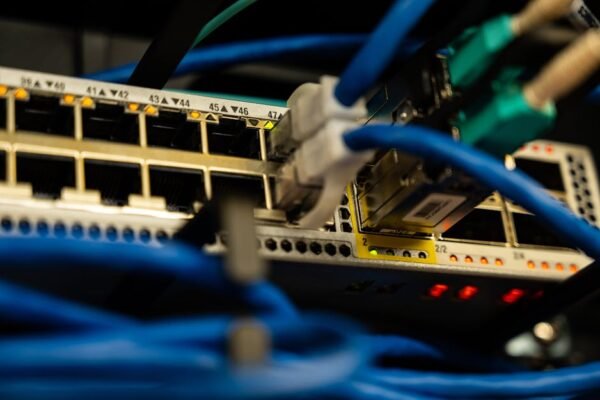
- A managed switch — if you want VLANs (and you will), a basic managed switch like a TP-Link TL-SG108E handles 802.1Q tagging for under $40.
Setting Up Firewall Rules: The Basics
Once your firewall is installed and you can reach the web interface, the first thing to do is build your ruleset. Both pfSense and OPNsense use the same core concept: rules are evaluated top-to-bottom on each interface (see our VLAN segmentation) (see our Cisco Catalyst vs Meraki), and the first matching rule wins.
Here are the fundamental firewall rules I configure on every installation:
WAN Interface (Internet-Facing)
- Block all inbound by default. This should already be the case, but verify it. No unsolicited traffic from the internet should reach your LAN.
- Block bogon and private networks on WAN. Both pfSense and OPNsense have checkboxes for this. It prevents spoofed traffic using reserved IP ranges from entering through your WAN port.
- Allow only specific inbound rules you explicitly need — for example, a port forward for your WireGuard VPN (typically UDP 51820).
LAN Interface (Your Trusted Network)
- Allow LAN to access the internet. The default LAN rule in both platforms usually permits this. Keep it, but consider tightening it over time.
- Block LAN from accessing the firewall admin interface on non-management ports. You do not want a compromised IoT device poking at your firewall dashboard.
- Create separate VLANs for device categories. I use VLAN 10 for trusted devices (laptops, phones), VLAN 20 for IoT (cameras, smart speakers), and VLAN 30 for a guest network. Each VLAN gets its own firewall rules.
Example: Isolating IoT Devices
Here is the logic for an IoT VLAN firewall rule in OPNsense. The goal is to let IoT devices reach the internet but prevent them from accessing your trusted LAN or the firewall itself:
# IoT VLAN rules (evaluated top to bottom)
1. BLOCK | IoT Net -> LAN Net | Any | Block IoT from reaching trusted LAN
2. BLOCK | IoT Net -> This Firewall | Any | Block IoT from accessing the firewall
3. ALLOW | IoT Net -> !RFC1918 | Any | Allow IoT to reach the internet only
4. BLOCK | IoT Net -> Any | Any | Default deny everything elseRule 3 uses the negation of RFC1918 private address ranges, which effectively means “allow traffic only to public internet addresses.” This is a clean way to give devices internet access while keeping them off your internal networks.
WireGuard VPN: Secure Remote Access Done Right
One of the best upgrades you can make to your home network security is setting up a VPN server for secure remote access. WireGuard VPN is the modern answer, dramatically simpler than OpenVPN’s complex certificate authorities. It is built into the Linux kernel, uses state-of-the-art cryptography (Curve25519, ChaCha20, Poly1305), has a tiny attack surface (around 4,000 lines of code versus OpenVPN’s 100,000+), and connects almost instantly.
Setting Up WireGuard on OPNsense
OPNsense includes WireGuard as a built-in feature. Here is how I set mine up:
- Navigate to VPN → WireGuard → Instances and create a new instance (this is your server).
- Generate a key pair. OPNsense does this automatically when you create an instance.
- Set the listen port to 51820 (or any port you prefer).
- Assign a tunnel address, for example
10.10.10.1/24. - Under Peers, add each client device. Each peer gets its own key pair and an IP within the tunnel subnet (e.g.,
10.10.10.2/32). - Create a WAN firewall rule allowing UDP traffic on port 51820.
- Create a rule on the WireGuard interface allowing traffic from the tunnel subnet to your LAN (or wherever you want VPN clients to reach).
Client Configuration
On your phone or laptop, install the WireGuard app and create a config file like this:
[Interface]
PrivateKey = <client-private-key>
Address = 10.10.10.2/32
DNS = 10.10.10.1
[Peer]
PublicKey = <server-public-key>
Endpoint = your-home-ip:51820
AllowedIPs = 0.0.0.0/0
PersistentKeepalive = 25Setting AllowedIPs = 0.0.0.0/0 routes all your traffic through the home tunnel, which is what you want on public Wi-Fi. If you only need access to your LAN, replace it with your home subnet, like 192.168.1.0/24, 10.10.10.0/24.
With WireGuard running, I can access my home lab, check security cameras, and use my Pi-hole DNS from anywhere, all encrypted end to end.
Intrusion Detection with Suricata (or Snort)
A firewall controls what traffic is allowed, but an Intrusion Detection System (IDS) inspects the content of that traffic for malicious patterns. Think of it this way: the firewall is the bouncer checking IDs at the door, and the IDS is the security camera watching what people do once they are inside.
Suricata IDS is my recommended choice for home use. It is open source, supports multi-threaded inspection, and is available as a plugin in both pfSense and OPNsense. Snort is the other popular option, but Suricata’s multi-threading gives it better performance on modern multi-core hardware.
IDS vs. IPS: What Is the Difference?
- IDS (Intrusion Detection System) — monitors traffic and generates alerts when it detects something suspicious. It does not block anything; it just tells you.
- IPS (Intrusion Prevention System) — actively blocks traffic that matches a threat signature. Same engine, but it drops malicious packets in real time.
I recommend starting in IDS mode. Run it for a week or two, review the alerts, and tune out the false positives before switching to IPS mode. If you flip on IPS immediately without tuning, you will almost certainly break something, like a video call being flagged as suspicious or a gaming service getting blocked.
Getting Started with Suricata on OPNsense
- Install the
os-suricataplugin from System → Firmware → Plugins. - Navigate to Services → Intrusion Detection → Administration.
- Enable Suricata and select the interfaces to monitor (typically WAN and LAN).
- Under the Download tab, enable rulesets. I recommend starting with ET Open (Emerging Threats Open), which is free and covers a wide range of threats including malware, exploit attempts, and command-and-control traffic.
- Set the pattern matcher to Aho-Corasick for best performance.
- Click Download & Update Rules, then start the service.
Once running, check the Alerts tab regularly. You will likely see things like outbound DNS queries to known malicious domains, port scans from random internet hosts, and the occasional false positive from legitimate services. For each false positive, you can disable the specific rule SID (Signature ID) to clean up your alert feed.
How Much Hardware Does Suricata Need?
Suricata is more resource-hungry than the firewall itself. For connections under 1 Gbps, plan for at least an Intel Celeron N5105 and 8 GB of RAM. For gigabit+ with full IPS, step up to an Intel Core i3 or Ryzen Embedded with 16 GB.
DNS Security: DoH, DoT, and Why It Matters
Traditional DNS queries are sent in plain text, meaning your ISP and anyone on the network path can see every domain you visit. Even with HTTPS encrypting page content, DNS leaks your browsing patterns. Fixing this is one of the easiest wins in network security basics.
DNS over TLS (DoT) and DNS over HTTPS (DoH)
- DNS over TLS (DoT) encrypts DNS queries using TLS on port 853. It is easy for firewalls to identify and manage because it uses a dedicated port.
- DNS over HTTPS (DoH) wraps DNS queries inside regular HTTPS traffic on port 443. It is harder to distinguish from normal web browsing, which makes it more resistant to blocking but also harder to monitor.
For a home firewall setup, I recommend configuring your firewall to use DNS over TLS to an upstream resolver like Cloudflare (1.1.1.1) or Quad9 (9.9.9.9). Both pfSense and OPNsense support this natively under their DNS resolver settings (Unbound). Here is how to set it up on OPNsense:
- Navigate to Services → Unbound DNS → General.
- Under Custom Options, add forwarding configuration with TLS enabled:
server:
tls-cert-bundle: "/etc/ssl/cert.pem"
forward-zone:
name: "."
forward-tls-upstream: yes
forward-addr: 1.1.1.1@853#cloudflare-dns.com
forward-addr: 1.0.0.1@853#cloudflare-dns.com
forward-addr: 9.9.9.9@853#dns.quad9.netIf you are running Pi-hole alongside your firewall (which I covered in a previous post), you can configure Pi-hole to use your firewall as its upstream DNS, which in turn uses DoT to reach Cloudflare or Quad9. This gives you both ad blocking and encrypted DNS in a layered setup.
Blocking Unauthorized DNS
One important step many people miss: even after configuring encrypted DNS, devices on your network might still use their own hardcoded DNS servers (like Google’s 8.8.8.8). Create a firewall rule that blocks all outbound DNS traffic (TCP/UDP port 53) not originating from your firewall. This forces every device to use your secured resolver.
Network Monitoring: Seeing What Is Happening
Security is not a set-it-and-forget-it deal. You need visibility into what your network is doing. Here are the monitoring tools I rely on:
- Firewall logs — both pfSense and OPNsense log blocked and allowed connections. Review these weekly, especially the blocked entries on your WAN interface. You will be surprised how much unsolicited traffic hits your public IP.
- Suricata alerts — your IDS alert feed is a goldmine. After tuning out false positives, what remains is worth investigating.
- Ntopng — available as a plugin on both platforms, ntopng gives you real-time traffic analysis, top talkers, protocol breakdowns, and historical flow data. I run it on my OPNsense box and check it a few times a week.
- Grafana + InfluxDB — for the dashboard enthusiasts, you can export firewall and IDS metrics to InfluxDB and build beautiful Grafana dashboards. It is optional but incredibly satisfying to see your network data visualized over time.
At a minimum, set up email or push notifications for critical Suricata alerts. OPNsense supports this natively, and you can use services like Ntfy or Gotify for self-hosted push notifications to your phone.
Quick Wins Checklist: Lock Down Your Network Today
If the full firewall-VPN-IDS stack feels like a lot to tackle at once, here is a prioritized checklist. Start at the top and work your way down. Even implementing the first three items will dramatically improve your home network security:
- Change your router admin password from the default. Right now. I will wait.
- Update your router firmware (or your firewall if you have already upgraded). Check for updates monthly.
- Enable WPA3 on your Wi-Fi (or WPA2-AES at minimum). Disable WPS, which is a known attack vector.
- Replace your ISP router with a dedicated firewall running pfSense or OPNsense. Put the ISP router in bridge mode or use it only as a modem.
- Segment your network with VLANs. At minimum, separate your trusted devices from IoT devices and guests.
- Set up WireGuard VPN for secure remote access instead of exposing services directly to the internet.
- Enable DNS over TLS on your firewall’s DNS resolver.
- Block unauthorized outbound DNS (port 53) from all devices except your firewall.
- Install Suricata IDS and subscribe to the ET Open ruleset. Run in detection mode first.
- Set up monitoring and alerts. Even basic email notifications for critical IDS alerts are better than nothing.
- Disable UPnP on your firewall. UPnP lets devices punch holes in your firewall automatically, which is convenient but dangerous.
- Review your firewall rules quarterly. Remove anything you no longer need. The fewer open doors, the better.
Where to Go from Here
This guide covers the network security basics that I believe every home network should have in 2026. But security is a layered game, and there is always more to explore. Once you have the foundation in place, consider looking into:
- Network segmentation with 802.1X — authenticate devices before they even get a VLAN assignment.
- Certificate-based authentication for your WireGuard or OpenVPN connections.
- Automated threat intelligence feeds — pfBlockerNG (pfSense) or the built-in blocklists in OPNsense can block traffic to and from known malicious IPs and domains.
- Security Information and Event Management (SIEM) — tools like Wazuh or Security Onion aggregate logs from your firewall, IDS, and endpoints into a single pane of glass.
- Regular penetration testing — run Nmap scans against your own public IP from outside your network to verify that nothing unexpected is exposed.
The most important thing is to start. Replace your ISP router, set up a proper firewall, add WireGuard, and grow from there. Every layer you add makes your network meaningfully harder to compromise. If you have questions or want to share your own setup, drop a comment below.